According to GlobalWebIndex reports, an average PC user has 7.6 social media profiles. We are only talking about social platforms here, without taking into account work-related services and email clients.
However, this alone is enough to create a realistic picture of just how exposed we are online. Our personal data, passwords, financial information, pictures, and videos are stored on various third-party services and technically, we have no real control over this data.
Considering invasive marketing technology and active use of big data by businesses, it’s safe to say that any content, published online, can be used against you. The moderate consequences are pop-ups, targeted advertising on Youtube or Facebook. However, the stakes can also be much higher. If a hacker receives access to your credit card data, you can only imagine what kind of damage can be inflicted.
Table of Contents
Top 10 Methods For Securing Your Online Profiles
We analyzed the majority of the common online security threats and collected hacks on boosting your personal online security. Some of those are essential basic methods that, nevermind their simplicity, still, get ignored quite often. Some of these methods are more elaborate and will be of large interest to proficient PC users.
Tip #1 – Install and Update your Security Software
Having an antivirus tool is not a luxury but a common sense these days. Whether you are simply browsing online or downloading a new application, you can catch viruses, trojans, or spyware. Detecting those threats manually is difficult even for security enthusiasts, while for beginning users it would definitely be an impossible mission.
You can start with a free tool such as, for instance, Avast standalone download tool. It’s a great solution if you are not sure yet what product to pick. By trial-and-error, you can clearly see the advantages and disadvantages in regards to your computer.
Why is analyzing the software precisely on your device so important? Well, there are several reasons. First and foremost, sometimes a tool turns out to be incompatible with an operating system. Could be, your OS is not set up properly. Also, the software that you’ve already installed can get block the antivirus and lead to an unwarned shutdown. By checking these issues with a trial version instead of jumping straight ahead into buying a paid subscription, you ensure that there are no unexpected technical issues.
Tip #2 – Get a Web Extension on your Browser
If you are an active user of Google Chrome or Mozilla Firefox, you are probably already using a wide range of extensions. Generally, the best choice is to download the extension of the same antivirus that you have as a desktop version. Avast, for instance, has free web extensions for Chrome and Firefox.
Of course, if your desktop security provider does not have a web version, you can download a new security client. Selecting the extension, make sure that it provides one-and-all protection against all common types of online threats, including ad-trackers, malvertising, phishing tools, and spyware.
Additional features may include:
- A website rating service – a built-in tool that gives a security score for each opened page
- A quick warning whenever the website or a downloaded file may be dangerous
- Login and password management tools
- Ad-blocker.
If your web extension is developed by the same company as your desktop too, you can usually synchronize the two tools to perform integrated scannings and receive comprehensive reports.
Tip #3 – Prefer a Two-step Verification Whenever Possible
Don’t get lazy and choose elaborate security settings whenever you are presented with an opportunity. The majority of users, unfortunately, tend to ignore this simple precaution which makes further phishing a lot easier.
Most likely, you are already using such a system on banking services or medical platforms. If your emails contain a lot of confidential information, opting for a more elaborate access system is a must.
With the two-step verification, even a correctly entered password is not enough to access the account. The service will automatically send a random code to your phone number. If you entered the combination correctly, the access will be allowed. Since it’s difficult for a distant hacker to obtain access to your phone as well, a two-step verification system provides bulletproof protection.
Tip #4 – Pay Attention to Notifications
Most services hurry to alert their users whenever a third-party has penetrated the account. If someone enters the account from another device your location, you will receive a notification to your email. Pay attention to such messages – whenever you are not sure that you were indeed the one to access the website, go to the platform and change access credentials.
A little hack: such notifications can often fall to a ‘Promotions‘ tab. Be sure to check those occasionally to make sure you don’t miss any critical alerts.
Tip #5 – Install a Powerful Encrypting Tool
The most secure method to protect sensitive text files, messages, emails, and media is to encrypt this information with secure two-side encryption software. You can upload sensitive data directly to the program and the application will provide you with an encoded output. Rewrite the main file and paste the encrypted version instead of the actual one.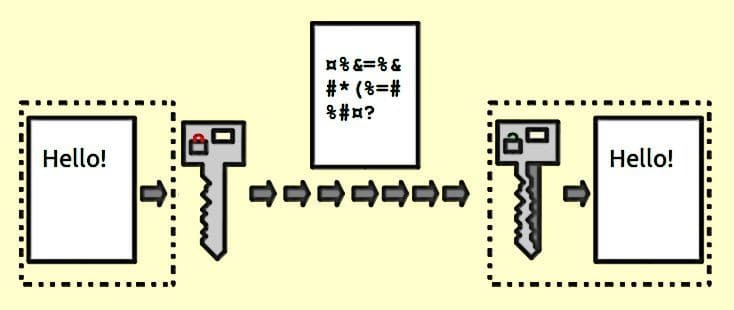
Whenever you need to access encoded content, go to the tool, enter a code, and decipher the information. This system can be also adopted to emails. You can paste the text of the message into the encryptor, provide the receiver with a key, and exchange encoded emails.
Tip #6 – Use cloud backup, firewalls, and parental control (if there are kids involved)
To make sure that your data is completely safe from unwanted attention, you need additional resources. First and foremost, protect important data from kids. If a kid sends someone your financial information or a confidential document to someone by a mistake, you will have only yourself to blame.
After all, there is an easy possibility to avoid these issues by installing antivirus software with a parental control feature. If your security client does not provide this feature by default, install a dedicated parental control. Such software allows putting content filters, tracking the amount of time, spent online, and restrict the number of visits to certain websites (social media or gaming platforms, for instance).
Firewalls make sure no one can breach to your PC from an outside network. Firewall blocks any kind of unwanted outbound traffic, making your PC impenetrable.
Cloud backup automatically copies all important files and stores them on a secure online server. However, the word ‘secure’ should be really emphasized here. Make sure that the tool uses peer-to-peer encryption (so even the development team cannot access the data). The governmental encryption standard is AES-256, and it’s also the most common one.
Tip #7 – Install a VPN to Bypass Censorship and Protect your Location
Sometimes we need to go to potentially dangerous websites or get access to censored pages. The safe way to do it is installing a secure VPN tool. Such services support dozens of international locations and allow connecting to any of them at any given moment.
Even though the temptation of choosing a hassle-free toll that requires no password protection and identification is quite strong, it’s safer to opt for a better-protected version.
Tip #8 – Install Antivirus Software on your Smartphone
Even though the majority of devices have built-in protection applications, it’s better to go an extra mile and install a custom tool that fits your particular needs. If you are a frequent online shopper, you need to choose an app that specialized in securing financial information.
If you have sensitive photos or videos, download secure Cloud storage and transfer all potentially critical files there. However, if you are a beginning smartphone user, go for a general all-in-one tool that protects each of these content types but a lesser extent.
Tip #9 – Use fewer messengers
Those who use WhatsApp, Facebook Messenger, Telegram, Viber, and other additional tools simultaneously, are naturally exposing themselves to the higher number of potential attacks. Some software, like Viber, can be used by marketers for promotion, and spam links, as we know, often tend to be malicious.
If you are using several messenger accounts, you will eventually stop checking your security status and the threat of falling victim to a data breach is generally higher.
Tip #10 – Additional DNS protection for Cloud services
This method will be useful for business owners and security managers of big corporations. If you store the sensitive business data on a third-party server, you want to take an extra step and create an additional protection level.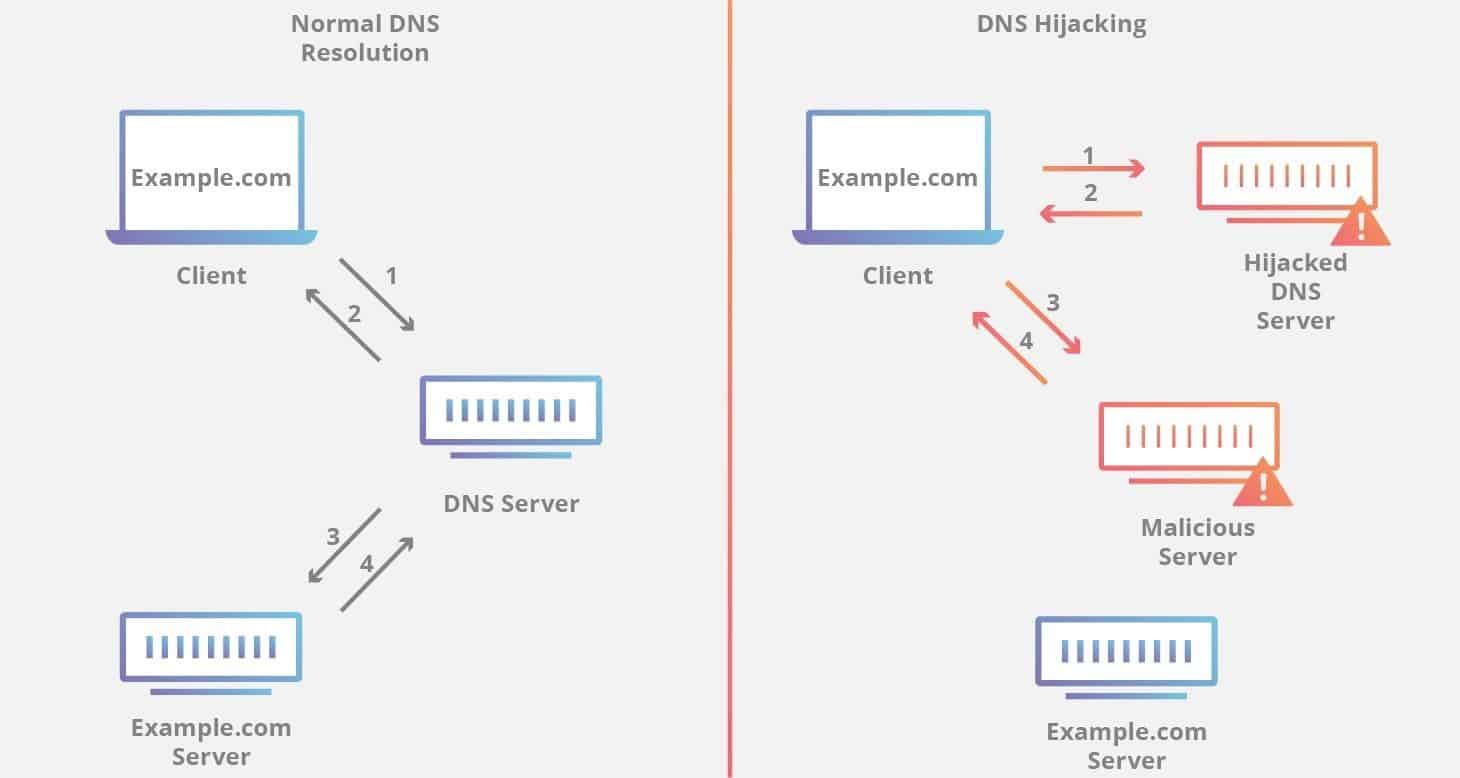
This can be done via paid security tools – a lot of them include a well-rounded Web Getaway protection. When the data on your clients, partners, and employees can be at stake, security is not the matter where management should cut corners.
Conclusions
- An average PC user has up to 10 online accounts. Maintaining each of them safe manually is difficult work. Therefore, automation is key.
- The first step to automating security is installing a reliable antivirus. Make sure your selected service can spot a phishing threat, rootkits, spyware, and malicious ads.
- For a higher level of online protection, install an antivirus extension directly to your browser. You will receive detailed information on websites’ security and the access to potentially dangerous pages will be prevented automatically.
- Download an encryption tool to encode sensitive information.
- Apply two-step verification whenever possible.
- Protect your personal data and information on the location via a reliable VPN service.
